As 2022 drew to a close, a hospital in New Jersey found itself in an unfortunate time warp of sorts. CentraState Medical Center was hit by a ransomware attack. Within minutes, everything that would normally be handled digitally in the 21st century reverted to workflows more reminiscent of the 1970s.
Lab orders, X-ray requests, prescriptions and the like were all suddenly relegated to manual, paper-based processes while hackers held CentraState’s network hostage. Computers and phones failed. Wait times in the emergency room soared. Incoming patients were diverted to other hospitals. Operations ground to a near standstill and wouldn’t return to normal for 12 harrowing days. Sadly, CentraState’s story is increasingly common.

Cyberattacks Come to Healthcare
According to the FBI, 25% of known ransomware attacks in 2022 targeted healthcare organizations. More often than not, those attacks were successful.
A report from Sophos titled “The State of Ransomware in Healthcare 2022” found that roughly 60% of ransomware attacks on healthcare organizations result in the encryption of data. When these distributed denial of service (DDoS) attacks occur, normal hospital operations are suspended, costs resulting from inefficiency accumulate and patient safety is put at risk.
There is also the matter of the ransom itself. While the average ransom paid by U.S. healthcare organizations ($197,000) is lower than for corporations as a whole ($800,000), hospitals are paying more often. It is believed that 70% of hospitals end up paying hackers the ransom demanded out of sheer necessity. Everything from operating rooms to pill dispensing machines are now computerized. With each minute that passes, the ability to provide patient care hangs in the balance.

Cybersecurity and the Candy Bar Effect
Until now, hospitals have pinned their hopes on making their networks as impenetrable to attack as possible. Chester Wisniewski, field chief technology officer of applied research at Sophos, compares this scenario to a candy bar.
“There’s a hard outer shell, and there’s a soft, gooey center,” Wisniewski says. “So if the criminals can get access to that outside barrier, once they’re on the inside, they kind of have carte blanche access typically to the entire network … I mean, patient records, what you’re allergic to, what pills you get on what schedule.”
Unfortunately, history shows that the hard outer shell will always be vulnerable. “No matter what they do, how much they invest – because of the complexity of the technology,” says John Riggi, former FBI agent and national advisor for cybersecurity and risk at the American Hospital Association. “The way that adversaries are able to get phishing emails into organizations ultimately depends upon the human factor – the weakest link we often say in the field.”
Tom Gordon, senior vice president and chief information officer for Vitua Health, agrees with this assessment. “You can have the best perimeter defenses, but if somebody’s giving away their credentials, those defenses really don’t mean anything.”
Planning for the Inevitable
Ransomware attacks are on the rise and all network defenses are ultimately vulnerable. Knowing this, hospitals must plan for the inevitable. Our prior blog on the topic describes three ways to defend against hospital ransomware attacks. Two of those solutions seek to minimize the likelihood or scope of an attack:
1: Employee training
Security awareness training for hospital staff has been proven to strengthen the “weakest link” mentioned by Riggi above.
2: Network segmentation
Dividing a hospital’s computer network into smaller sections with minimal inter-connectivity limits how many vital systems can be impacted by the cybercriminal.
However, the third defense assumes the attack will be successful and, instead, focuses on blunting the impact on patient care.
3: System back-ups
Backing up vital IT system data – including a copy that is stored entirely offline – enables a hospital to quickly rebuild its technology systems. Doing so shortens the unplanned downtime period experienced and means the hospital is no longer at the mercy of cybercriminals to recover.
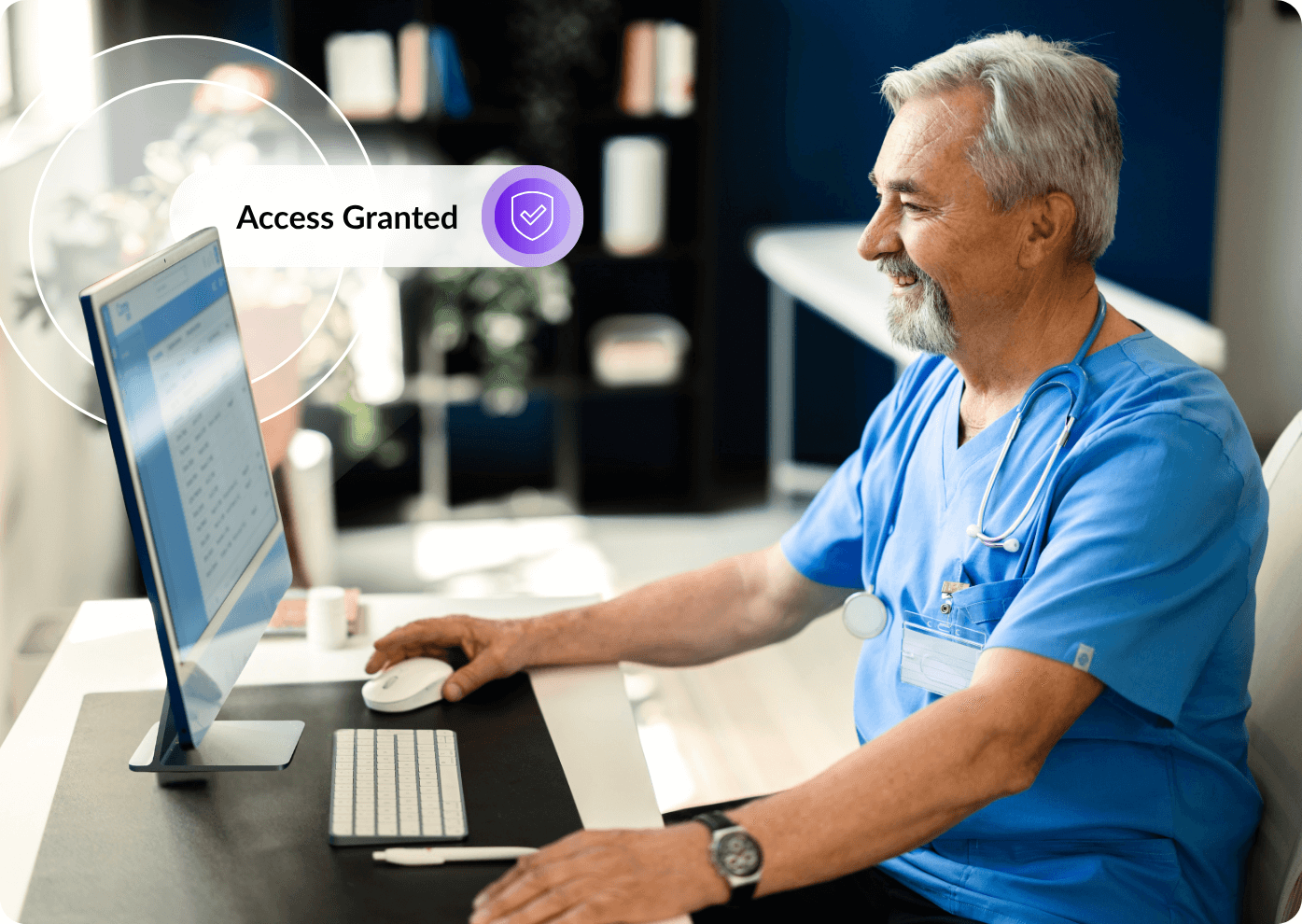
A somewhat similar approach can be applied to a healthcare system’s EHR. iMedDowntime by Taylor Healthcare is engineered to complement a hospital’s EHR during unscheduled downtime periods like those resulting from a ransomware attack.
With iMedDowntime, a hospital or clinic can maintain normal operations without sacrificing efficiency or the quality of patient care – regardless of the status of its network or power supply.
- Registrars can search patient records and print admissions packets while the admission, discharge and transfer (ADT) system is down.
- Nurses can print forms, wristbands and labels, complete with patient demographics and barcodes.
- Physicians can access condition-specific protocols and continue to provide the same level of care as if the network was still live.
iMedDowntime allows hospital and clinic staff to access and print the critical documents needed to sustain operations during a successful ransomware attack. If the attacks themselves cannot be prevented, iMedDowntime gives healthcare organizations another way to respond.




/Blog%20Body%20Image%20%E2%80%93%20Ransomware%20Defend.jpg)